Трафик VLAN через OpenVPN, LAN через основной шлюз.
Добавлено: 03 июл 2025, 10:30
Nacho
Здравствуйте.
Не получается пустить трафик с VLAN через OpenVPN, а LAN через основной шлюз.
ROS 7.19.2
Схема: на ether1 приходит интернет по DHCP 10.2.0.1. Подключен openVPN клиент. Vlan настроен на бридже. Есть локальная сеть 192.168.88.0/24 и для vlan 10.10.2.0/24. На Vlan работает Wifi и все его клиенты должны идти через впн, остальные нет.
Через mangle маркирую всю сеть 10.10.2.0/24, в route list маршруту впн ставлю метку из mangle. С телефона подключаюсь к вайфаю, получаю айпи из сети 10.10.2.0/24 и вроде как, трафик идет через впн (сейчас почему не работает..). А вот ПК из сети 192.168.88.0/24 сеть не видит. (пингов до внешних ресурсов нет).
Опирался на этот гайд: viewtopic.php?p=31356#p31356
У меня какая то непонятка с правилами NAT и mangle.
Прошу помощи, спасибо!
Не получается пустить трафик с VLAN через OpenVPN, а LAN через основной шлюз.
ROS 7.19.2
Схема: на ether1 приходит интернет по DHCP 10.2.0.1. Подключен openVPN клиент. Vlan настроен на бридже. Есть локальная сеть 192.168.88.0/24 и для vlan 10.10.2.0/24. На Vlan работает Wifi и все его клиенты должны идти через впн, остальные нет.
Через mangle маркирую всю сеть 10.10.2.0/24, в route list маршруту впн ставлю метку из mangle. С телефона подключаюсь к вайфаю, получаю айпи из сети 10.10.2.0/24 и вроде как, трафик идет через впн (сейчас почему не работает..). А вот ПК из сети 192.168.88.0/24 сеть не видит. (пингов до внешних ресурсов нет).
Опирался на этот гайд: viewtopic.php?p=31356#p31356
У меня какая то непонятка с правилами NAT и mangle.
Код: Выделить всё
# 2025-07-03 10:28:08 by RouterOS 7.19.2
/interface bridge
add admin-mac= auto-mac=no comment=defconf name=bridge \
vlan-filtering=yes
/interface ovpn-client
add auth=sha256 certificate=cert_ovpn-import1750322870 cipher=aes256-gcm \
connect-to=5.129.х.х mac-address=FE:CD:A0:36:57:0B name=ovpn protocol=\
udp user=ovpnuser verify-server-certificate=yes
/interface vlan
add interface=bridge name=vlan20 vlan-id=20
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
add name=WAN2
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
add authentication-types=wpa2-psk mode=dynamic-keys name=test \
supplicant-identity=""
/interface wireless
set [ find default-name=wlan1 ] band=2ghz-b/g/n channel-width=20/40mhz-XX \
disabled=no distance=indoors frequency=auto mode=ap-bridge \
security-profile=test ssid=MikroTik-DB8B25 vlan-id=20 vlan-mode=use-tag \
wireless-protocol=802.11
set [ find default-name=wlan2 ] band=5ghz-a/n/ac channel-width=\
20/40/80mhz-XXXX distance=indoors frequency=auto mode=ap-bridge \
security-profile=test ssid=MikroTik-DB8B25 wireless-protocol=802.11
/ip hotspot profile
set [ find default=yes ] html-directory=hotspot
/ip pool
add name=default-dhcp ranges=192.168.88.10-192.168.88.254
add name=dhcp_pool1 ranges=10.10.1.2-10.10.1.254
add name=dhcp_pool2 ranges=10.10.2.2-10.10.2.254
/ip dhcp-server
add address-pool=default-dhcp interface=bridge name=defconf
add address-pool=dhcp_pool2 interface=vlan20 name=dhcp2
/routing table
add disabled=no fib name=vpn
add disabled=no fib name=NOvpn
/certificate settings
set builtin-trust-anchors=not-trusted
/disk settings
set auto-media-interface=bridge auto-media-sharing=yes auto-smb-sharing=yes
/interface bridge port
add bridge=bridge comment=defconf interface=ether3
add bridge=bridge comment=defconf interface=ether2
add bridge=bridge comment=defconf interface=ether4
add bridge=bridge comment=defconf interface=ether5
add bridge=bridge comment=defconf interface=wlan1
add bridge=bridge comment=defconf interface=wlan2
/ip neighbor discovery-settings
set discover-interface-list=LAN
/interface bridge vlan
add bridge=bridge tagged=ether2,wlan1,bridge vlan-ids=10
add bridge=bridge tagged=ether2,wlan1,bridge vlan-ids=20
/interface list member
add comment=defconf interface=bridge list=LAN
add comment=defconf interface=ether1 list=WAN
add interface=vlan20 list=LAN
add interface=ovpn list=WAN2
/ip address
add address=192.168.88.1/24 comment=defconf interface=bridge network=\
192.168.88.0
add address=10.10.1.1/24 interface=*A network=10.10.1.0
add address=10.10.2.1/24 interface=vlan20 network=10.10.2.0
/ip dhcp-client
add add-default-route=no comment=defconf default-route-tables=main interface=\
ether1 use-peer-dns=no use-peer-ntp=no
/ip dhcp-server network
add address=10.10.2.0/24 comment=VLAN dns-server=10.10.2.1 gateway=10.10.2.1
add address=192.168.88.0/24 comment=LAN dns-server=192.168.88.1 gateway=\
192.168.88.1
/ip dns
set allow-remote-requests=yes servers=77.88.8.8
/ip dns static
add address=192.168.88.1 comment=defconf name=router.lan type=A
/ip firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked disabled=yes
add action=accept chain=input disabled=yes dst-port=1723 protocol=udp
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid disabled=yes
add action=accept chain=input comment="defconf: accept ICMP" disabled=yes \
protocol=icmp
add action=accept chain=input comment=\
"defconf: accept to local loopback (for CAPsMAN)" disabled=yes \
dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" \
disabled=yes in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
disabled=yes ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
disabled=yes ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related disabled=yes hw-offload=yes
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked disabled=yes
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid disabled=yes
add action=drop chain=forward comment=\
"defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat \
connection-state=new disabled=yes in-interface-list=WAN
add action=accept chain=forward disabled=yes in-interface=vlan20 \
out-interface=ether1
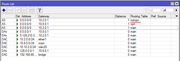
/ip firewall mangle
add action=mark-routing chain=prerouting new-routing-mark=vpn passthrough=no \
src-address=10.10.2.0/24
add action=mark-routing chain=prerouting disabled=yes new-routing-mark=main \
passthrough=no src-address=192.168.88.0/24
/ip firewall nat
add action=masquerade chain=srcnat out-interface-list=WAN to-addresses=\
10.2.0.14
add action=masquerade chain=srcnat out-interface-list=WAN2 routing-mark=vpn \
to-addresses=10.2.0.14
/ip route
add disabled=no distance=1 dst-address=0.0.0.0/0 gateway=10.2.0.1 \
routing-table=main scope=30 suppress-hw-offload=no target-scope=10
add disabled=no distance=1 dst-address=0.0.0.0/0 gateway=10.8.0.1 pref-src="" \
routing-table=vpn scope=30 suppress-hw-offload=no target-scope=10
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" \
dst-port=33434-33534 protocol=udp
add action=accept chain=input comment=\
"defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=\
udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 \
protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=input comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=\
!LAN
add action=fasttrack-connection chain=forward comment="defconf: fasttrack6" \
connection-state=established,related
add action=accept chain=forward comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment=\
"defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" \
hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=\
500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=forward comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=\
!LAN
/system clock
set time-zone-name=Europe/Moscow
/tool mac-server
set allowed-interface-list=LAN
/tool mac-server mac-winbox
set allowed-interface-list=LAN